Admin Firewall Deployment
Background?
Information System Security has been a key concern over the past many years as more and more business processes rely on Information Technology to operate. Alike many other organizations, the usual first line of defense would be Internet protection with security devices such as a perimeter firewall. However, this type of protection cannot address the challenges posed to network security for universities. Security enhancement at universities is even more challenging as security control and academic freedom, at certain extent, conflict with each other, and there are just too many devices connecting to the network with different purposes and usages.
To address these challenges, the Computing Services Centre (CSC) has been implementing internal admin firewalls to better segregate departmental networks and to guard undesirable internal traffic within the campus network.
These internal firewalls are Next Gen?eration Firewalls (NGFWs). NGFW provides additional protection comparing to the traditional ones which monitors traffic from Open Systems Interconnection (OSI) layer 2 (Data Link Layer) through layer 7 (Application Layer). Policies can be defined based on user and application, rather than low-level network ports and addressing. For example, NGFW includes integrated intrusion detection systems (IDS) and intrusion protection systems (IPS) that detect attacks based on traffic patterns, user behaviour, threat signatures, etc. These functionalities perform deeper inspection and improve packet-content filtering of network traffic up to the application layer.
Current Situation
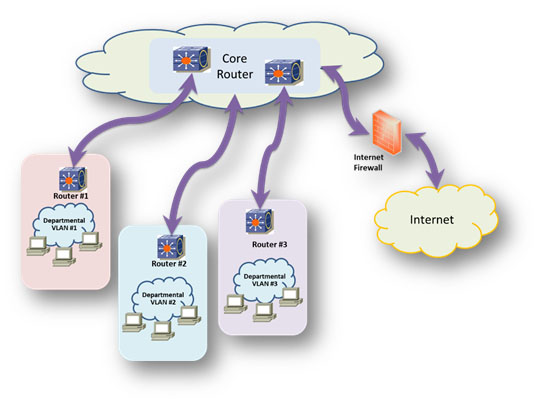
As shown in figure 1 below, the existing departmental networks are interconnected via the CityU campus Core network. Traffic can flow freely between the departmental networks; hence, if a workstation has been infected by virus / ransomware, workstations in another department may also get infected.
Admin Firewall Deployment Approach
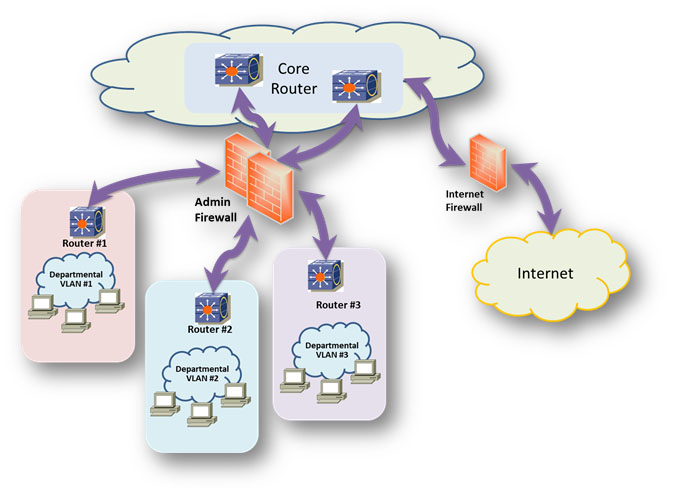
A pair of admin firewalls are deployed to mitigate similar threats and they will act as barriers between each departmental network and the CityU Core network.
Upon completion, firewall policies would be deployed to control the traffic flow amongst departmental networks. In principle, traffic will be allowed on a need basis, and the firewalls will block all unknown and unregistered inter-departmental traffic.
Diagram below shows the high-level design and the traffic flow after implementing the admin firewalls.
Migration Steps
The migration of each departmental network under the Admin Firewall protection will be done in several phases as listed in the table below:
|
# |
Phase |
Duration |
Description |
Objective |
|
1 |
Traffic re-route |
30 minutes |
Re-route departmental traffic to pass through the Admin Firewall |
Departmental traffic need to go through the Admin Firewall for inspection, classification, control and protection |
|
2 |
Monitoring |
Two weeks after migration |
Firewall will monitor but not block the traffic |
Learn the traffic pattern as the input to define firewall rulesets |
|
3 |
Firewall ruleset testing and fine-tuning |
At least four weeks after monitoring phase
|
Firewall rulesets will be implemented and allow all traffic by default unless controlled by rulesets |
Test and fine-tune the firewall rulesets |
|
4 |
Protecting |
After ruleset testing phase |
Firewall will protect the department and deny all traffic by default if the traffic is not allowed by the rulesets |
Protect the department with firewall rulesets |
Implementation Plan
The migration process will be conducted in sequence initially for administrative departments. The Central IT will be amongst the first to migrate to the firewall protected networks. After the Central IT migration, Internet of Things (IoT) networks such as the Car Park System and the EV Charger Systems will subsequently be migrated. Other administrative departments will follow.
??